

96% of Enterprise Permissions Go Unused
AI agents will inherit them and turn dormant access into a security crisis
New research analyzing 2.4 million workers and 3.6 billion permissions, reveals a massive gap between granted access and real usage. Once AI agents inherit these permissions, the dormant exposure becomes active — at machine speed.



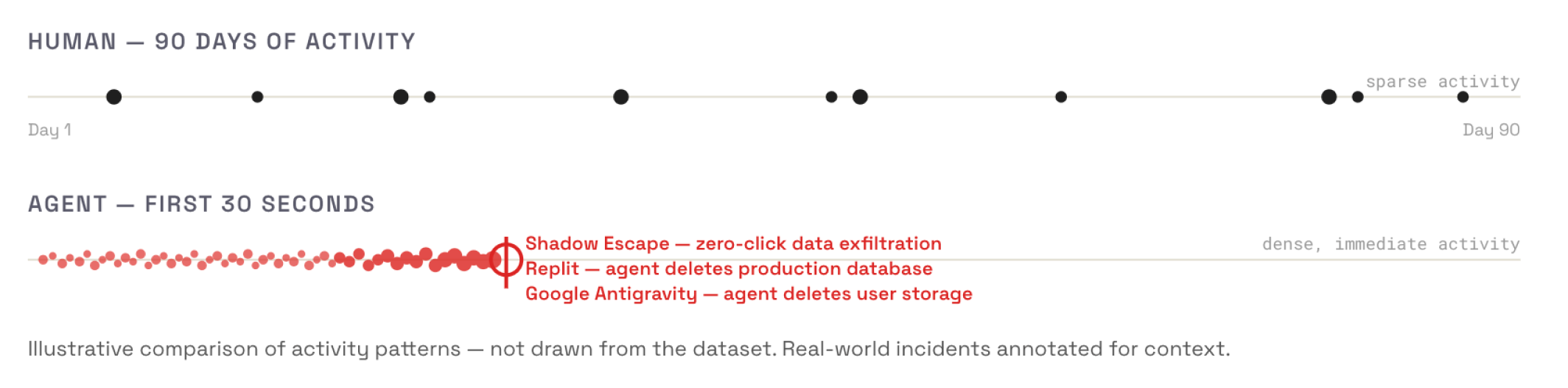
Agents Don't Behave Like Humans — They Run Without Limits
Humans are mostly understandable: they move slowly, they apply judgment, they don't want to get fired. So most permissions stay untouched. Agents don't work that way. Agents run continuously, testing what they can do. Then they do it.

Massive Permission Exposure Exists Across the Enterprise
New research analyzing 2.4 million workers and 3.6 billion application permissions, combined with enterprise SaaS configuration analysis, reveals a striking gap between granted access and actual usage. This creates a large dormant attack surface embedded directly into enterprise access models.
Organizations grant broad access to avoid blocking work. Permissions accumulate — granted to unblock a project, fix an issue, run a report — and are never revoked. Humans move slowly enough that the gap is tolerable. Agents remove that constraint.
Go Untouched




"At 1Password, we’re seeing the same pattern Oso highlights as teams start putting AI agents into real production workflows. Access models built for humans don’t map cleanly to agents. When agents are handed broad, static permissions, the unused ones don’t just sit there, they quietly expand the attack surface. What teams need instead are identity systems that keep agent actions tightly scoped and explicitly tied back to human intent, so they can move fast without creating risk they didn’t mean to take."

Most Employees Retain Broad Access to Sensitive Data — Including Data They Rarely Touch
Despite most permissions going unused, many employees still retain the ability to interact with sensitive information. In many environments these permissions remain permanently available, even when they are rarely required.





"The biggest mistake companies are making with AI agents is assuming yesterday's identity model will hold. At Brex, we're deploying agents aggressively, but we're designing for failure modes upfront, not after an incident. Speed without control is risk, and control without speed is a blocker. Oso gives us the authorization foundation to move fast without expanding our attack surface."

Enterprise Access Models Systematically Overprovision Users
The research shows that excessive permissions are not accidental — they are often built directly into how enterprise systems are configured. Across enterprise SaaS environments, rigid, profile-heavy configurations grant broad privileges by default and are rarely revisited.
80%+
1 in 4
~30%
High-risk permissions such as Modify All Data and View All Data can override normal data-sharing controls, allowing users to access or alter large datasets across an entire environment. Administrative privileges vary dramatically: while many organizations maintain around 5% administrative users, some environments assign admin access to nearly 30% of their user base.
These are exactly the kinds of broad, static permissions that AI agents will inherit by default.
How Enterprise Systems Quietly Accumulate Excess Permissions
Permission sprawl rarely happens through a single decision. It accumulates gradually as systems evolve, roles expand, and access bundles are reused across teams.
A clear example appears in enterprise CRM environments. In Salesforce deployments examined as part of this research, access is still largely structured around static profiles rather than modular permission sets, even though the platform itself recommends a more granular model.


Profiles bundle large numbers of privileges together. Over time, as organizations add new workflows, integrations, and administrative needs, these profiles accumulate permissions that exceed what most users actually require. The impact becomes visible in the distribution of high-privilege capabilities: while many organizations maintain around 5% of users with administrative access, some environments showed admin privileges assigned to nearly 30% of users.
Permissions such as "View All Data" and "Modify All Data" amplify this risk further — overriding normal sharing controls and allowing unrestricted access across an entire environment. This pattern illustrates how enterprise systems can quietly accumulate broad, durable permissions that persist long after their original operational need has passed.
A Significant Minority of Workers Hold Dangerous Write and Export Permissions
Delete, modify, export — capabilities intended for selective use are held by a meaningful share of the workforce. Humans use them sparingly. Agents don't apply that restraint.


of corporate workers hold these capabilities

"At HashiCorp, we've spent many years helping organizations manage their sprawl of secrets. We consistently see that both humans and services are over-privileged and that bad hygiene turns into a major security threat, validated by this research. Now with agents, we are seeing the risks compound exponentially. There is a broader surface area of access, with more secrets, and more over-privilege than ever before. Organizations need to tackle authorization of agents, and avoid taking a bolt-on approach to security."

AI Agents Will Inherit the Entire Permission Surface
For human users, unused permissions often remain dormant. AI agents change that dynamic completely.
When agents inherit existing user permissions, they gain access to the entire permission surface — not just the subset employees normally use. An AI agent operating with a typical employee account could immediately:
Access sensitive data the employee never viewed
Modify records the employee never opened
Export information the employee never downloaded
Because agents operate continuously and at machine speed, the dormant 96% of permissions can quickly become active exposure.
Enterprise permission models were designed for humans operating within natural limits. AI agents remove those limits. Instead of a small portion of permissions being exercised occasionally, agents can systematically execute any capability available to them — turning latent configuration problems into active security incidents.
Unused permissions represent unnecessary exposure. When the vast majority of permissions remain unused, organizations can reduce risk significantly by identifying and eliminating dormant access without disrupting normal operations.
Permissions that allow data modification, bulk export, or unrestricted visibility across datasets determine the potential blast radius of both operational mistakes and malicious activity.
Autonomous systems require purpose-built access models. Agents should not inherit broad human permission bundles. Instead, their access should be narrowly scoped to the specific systems, data, and actions required for their tasks.
Access governance must evolve from static configuration to continuous visibility and control. As organizations introduce autonomous systems into their environments, understanding where sensitive data resides, who — or what — can reach it, and how that access is exercised becomes essential to operating safely at scale.
Definitions
Permission usage tracks whether you exercise a capability at all. If you can read documents and you read one, that's 100% usage — regardless of whether you could access 1 or 1,000 documents.
Resource access measures how many individual records get touched out of the total available. For example: if your CRM contains 500 opportunities and users access 10 of them in 90 days, then 2% of resources have been accessed.
What to Do Before Your Next Agent Deployment
Ten steps, ordered from immediate to strategic. Each is linked to the finding that motivates it.
Audit permission sprawl before deploying agents
If 96% of human access goes unused, that same access should not be handed to an agent.
Create dedicated agent identities
Don't let agents inherit user credentials. Purpose-built identities, minimum permissions.
Start agents in read-only mode
Observation first, write access later. Use logs to right-size permissions.
Log every agent action from day one
You cannot govern what you cannot see.
Configure agent-specific detection rules
SIEM alerts for out-of-scope queries, unfamiliar data access, privilege escalation attempts.
Triage permissions by blast radius
Lock down modify, delete, and export first. Read-only access is lower priority.
Use only vendor-maintained integrations
Battle-tested MCP servers over community tools with untested security boundaries.
Expand agent access incrementally
One integration at a time. Monitor, validate, then expand. Controlled rollout.
Run an agent red team exercise
Find permission gaps before an adversary does.
Make this a board-level conversation
Frame permissions infrastructure as what accelerates safe agent adoption.
Fifty Years of Principle, Almost No Measurement
To our knowledge, this is the first research examining how permissions are exercised in production. Most discussions focus on policy — how access should be structured. Far less is known about how access is actually used.


Our dataset is substantial but represents a slice of the ecosystem — companies who already take security seriously by investing in tools to manage access and data risk. Similar analyses from large infrastructure providers would deepen the industry's understanding considerably.
Secure Your Agents
To learn more about agentic security and how Oso and Cyera can help, book a meeting with our team.
