Your engineers are already using agents
Next up is product, finance, and sales - the whole company. How do you get your arms around agent adoption?
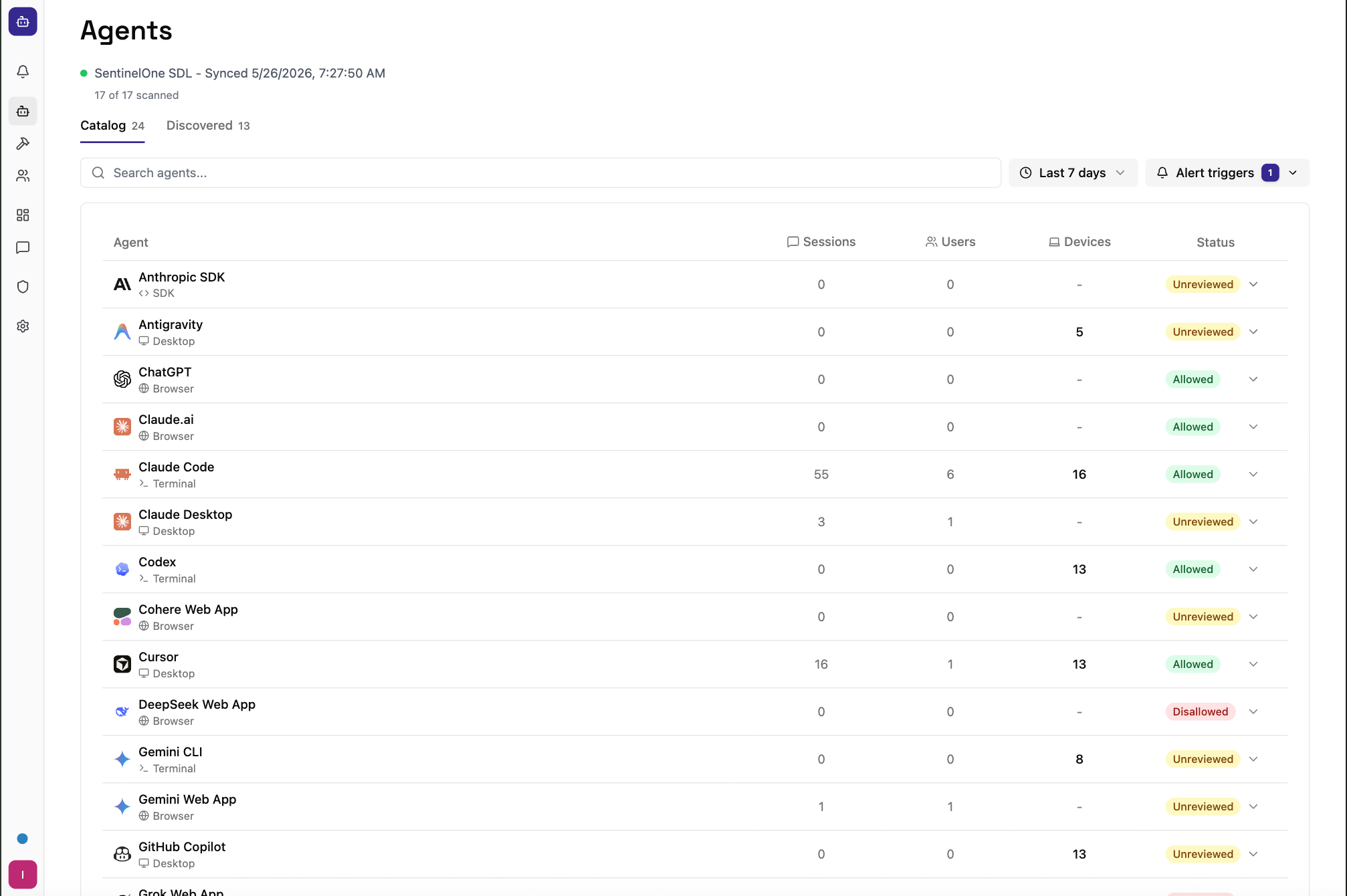


Integrated into your stack




















































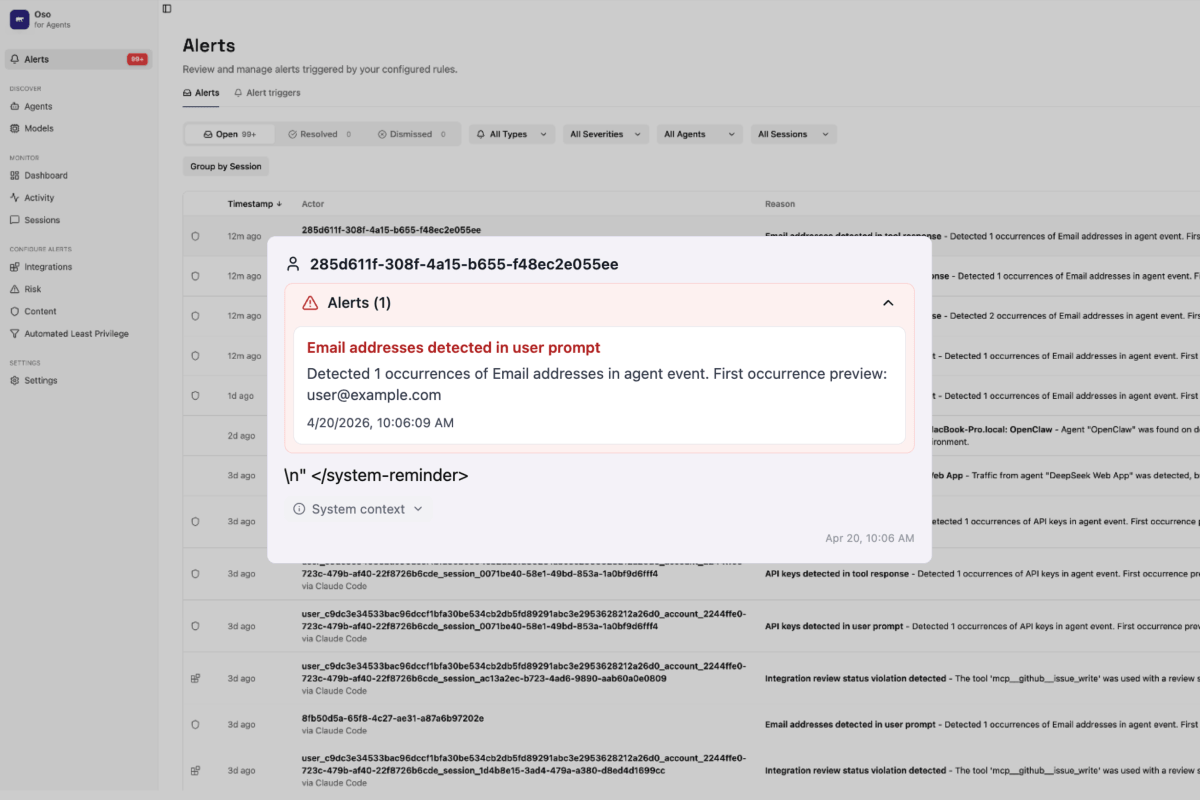
Real-world AI agent failures, exploits, and defenses

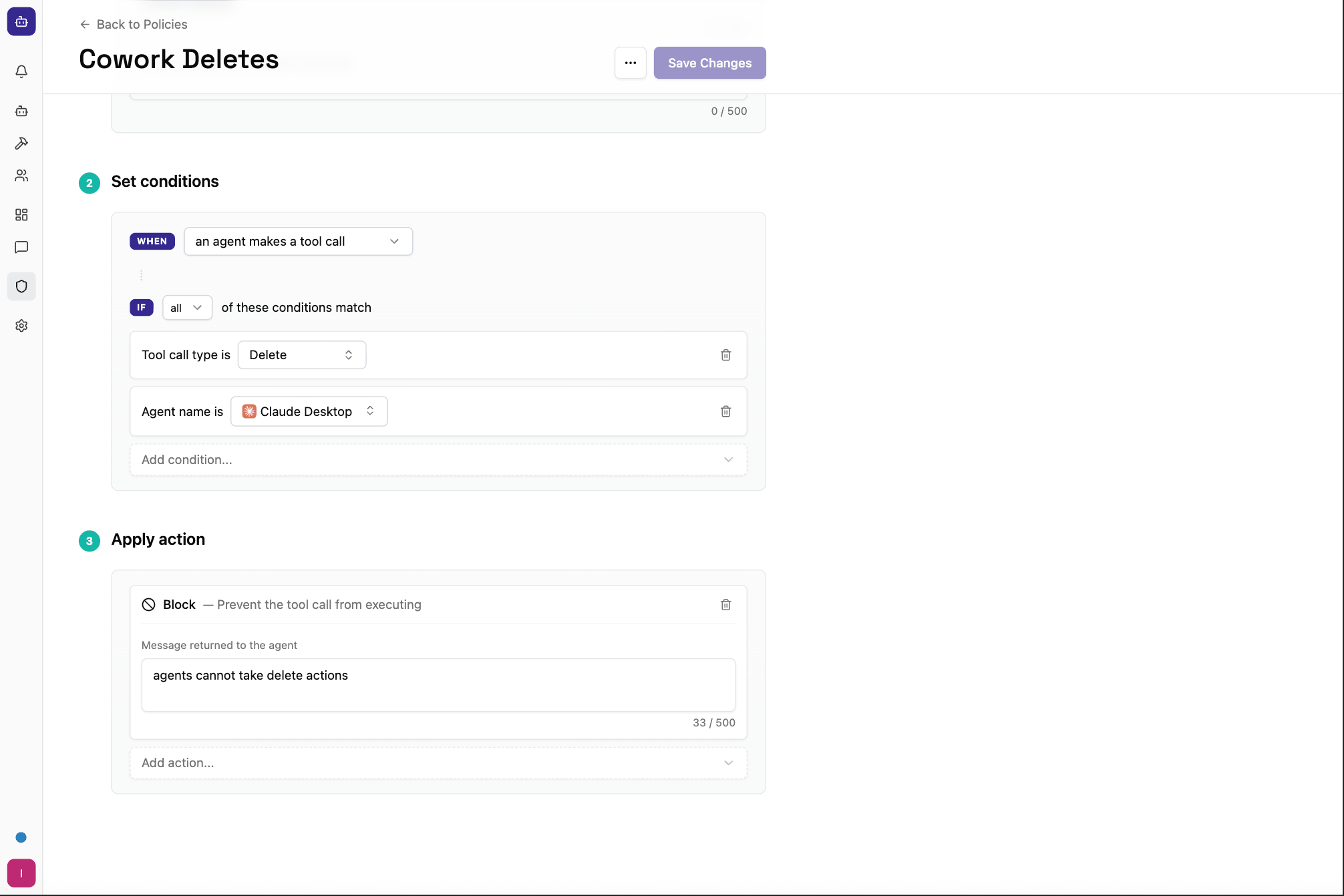
Least Privilege Manifesto
We’ve been doing permissions wrong. Not just a little wrong — completely wrong. And for humans, it mostly didn't matter. For agents, it's going to.
Your employees ignore 96% of their permissions. Agents won't.




























